The Maths Behind Bitcoin: Series Announced
You have all heard of this new form of money, these so-called cryptocurrencies. To my surprise, after I finished my maths PhD, I realised some of the maths I know is used to ensure the integrity and authenticity of Bitcoin transactions. It is the oldest and probably most successful cryptocurency to this day. Its 10-year anniversary was celebrated last month on January 03, 2019; on that day 10 years ago, the first block on the Bitcoin blockchain was mined.
Oh sh*t, I said the P word. Don’t leave just yet!
You will not need a PhD or any maths degree to understand the articles in this series. Pinky promise. The ambition is for you to understand what a private and a public key correspond to and where they come from.

Photo by Thought Catalog on Unsplash
First things first: what exactly is Bitcoin?
For the context of this series about the Maths Behind Bitcoin, we will think of Bitcoin as a big book of past transactions, which is often referred to as the ledger. A transaction for us will be the equivalent of a message:
Alice PAYS Bob 1 BTC.
It consists of a payer (Alice), a payee (Bob), and the amount (1 BTC). This transaction means that Alice’s balance should decrease by 1 BTC and that of Bob should increase by 1 BTC.
Alice’s balance is kept “inside” her wallet, and Bob’s in his. This transaction will be added to the ledger if Alice can actually spend that money.
One condition for Alice to spend the money is that this amount must be available in her wallet, or, more accurately, if Alice’s wallet controls enough money. It is then not possible to spend money you do not have; no credit card equivalent in the realms of Bitcoin. The ledger is all you need to verify how much Alice has: you can read through all the past transactions and count Alice’s credit operations and debit operations.
BALANCE = CREDIT - DEBIT
For example, if the ledger says
…
Peter PAYS Alice 2 BTC.
Alice PAYS Petunia 1 BTC.
…
it means Alice’s CREDIT is 2 BTC, and her DEBIT is 1 BTC. Therefore she can pay Bob at most 1 BTC.
This obviously is a simplification of what is really happening; we are not representing the possible fees going to the Bitcoin miners.
As an aside, miners play a very important role in the Bitcoin ecosystem. They should be rewarded as they ensure the security of the ledger: you would not want anyone to be able to rewrite the ledger so that they could erase debts and/or credit themselves with money they do not duly own. You can think of miners as transaction bouncers.

Stormtrooper surveilling passing Bitcoin transactions, Photo by John Moeses Bauan on Unsplash
To summarise, a wallet is just a piece of information enabling its holder to spend the funds, as the balance is recorded in the ledger. This essential piece of information is called a private key and it must be kept… private. If you re-read the first sentence of this paragraph, you see “enabling its holder to spend”. The security of your private key is of paramount importance; not only it should stay private – you don’t want Joe to spend your funds, but ensuring its integrity is necessary too.

Shit happens, Photo by Николай Егошин on Pixabay
Whoever controls the private key can then spend the available balance. Yes, all of it. On the flip side, if you lose access to your private key, you will effectively lose all your money. That’s why, for example, letting one individual control the keys of a crypto exchange is a pretty bad idea, even if it is the CEO.
Going back to our example, we took the private key to be people’s names. Hmmm, we could probably do better than taking publicly available information. Unless you are keeping your name private, it is not a viable solution: Bob could be tempted to write and add to the ledger
Alice PAYS Bob 1 BTC
if he knows Alice has 1 spare BTC. We would need something a bit more trustworthy to ensure that the consent of the payer is (stricly) taken into account. That something is Alice’s signature.
Who wants my digital-autograph?

Just imagine that you would like to pay by cheque. This cheque is a transaction with the field FROM: Alice pre-filled. There is a TO: field, an AMOUNT: field and room for a signature. Trying to cash in a cheque with the wrong signature would result in it being bounced by the bank, usually. The Bitcoin ledger will not accept a forged signature, never ever.
To sign a transaction, Alice uses her private key to generate a digital signature that proves her consent to this transaction, and to this exact transaction only. You see, Bob could be tempted to get more if he suddenly realised that Alice had meanwhile received a payment which brought her balance to 2 BTC. He could just change the message to be
Alice PAYS Bob 2 BTC.
Poor Bob, Bitcoin will not accept that other kind of forgery. Indeed, Alice’s digital signature is signing the message and the ledger will be able to verify if the signature is signing the message it accompanies. This is possible because Alice’s corresponding public key is available too.
Public Key Cryptography
Alice’s private key and the corresponding public key are what is called a key-pair. It is generated by a cryptographic system and provides a way to sign and verify some piece of information. This type of cryptography is called public key cryptography or asymmetric cryptography.
You are using it every day when browsing the web for instance. Yes, the locked lock in the URL bar of your browser (it is locked, right?) indicates that this blog has an SSL certificate properly set up (thank you, Let’s Encrypt), promising that your data is transferred securely over the Internet, because it is encrypted using a cryptographic key-pair.

Photo by Uwe Baumann on Pixabay
If there is anything you need to remember for now, let it be the following: public key cryptography is a system generating pairs of keys, one private, one public, with which it is possible to encrypt/decrypt and sign/verify a message.
With your pair of private 🔑 and public 🗝 keys, you can do:
-
encryption by
- encrypting with 🗝
- decrypting with 🔑
which is why people can send you encrypted emails with your public PGP key: since you are the only person holding the corresponding private key, no one could eavesdrop on your communication.
-
authentication by
- signing with 🔑
- verifying with 🗝
which is why people can be certain that you are the person behind this message they received: you sent the message along with a signature you generated specifically for that message, with your private key; the recipient can then verify the authenticity of your communication thanks to your public key.
ECDSA
In the context of Bitcoin, we are only interested in signing and verifying transactions. Signing and verifying transactions. Nothing. Is. Encrypted. So if you care a bit more about privacy (why should someone be able to find out that you paid 0.0005 BTC for an expensive cup of coffee last Tuesday around 4pm?), you would need to inquire privacy-focused cryptocurrencies like Monero or ZCash. You should also check out the future of Bitcoin, the rightly called ⚡Lightning Network.
Going back on track, the cryptographic system used for Bitcoin is called elliptic curve cryptography (ECC) and it relies on elliptic curves (ooh, did not see that one coming, did you?) and finite fields. And it sort of looks like this:
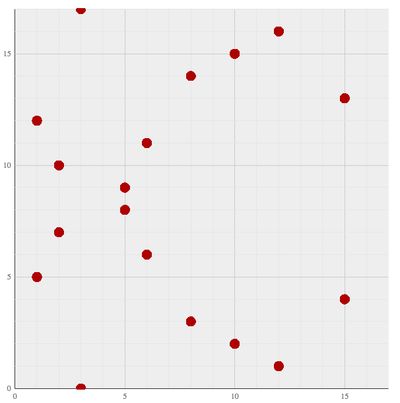
The ECDSA, or Elliptic Curve Digital Signing Algorithm, is the recipe to sign your coffee transactions with your shiny new key-pair generated by that cool elliptic curve. It also explains how to verify the authenticity and validity of the signature it provides.
What’s next
Believe me, you’re here for quite the ride. To understand one of the pillars of Bitcoin as a serious alternative to our current monetary system, we will journey through a diverse array of mathematical sceneries: sometimes, familiar landscape; sometimes, very exotic neighbourhoods. The list not being exhaustive, my hope is that, by the end of this series, you will learn about:
- basic geometry
- basic group theory
- basics of elliptic curves and their group structure
- basics of finite fields and elliptic curves defined over finite fields
so that in a grand final apotheosis, you will get to the Graal of knowledge: understand what your private and public keys really correspond to and how they are used together to ensure you are the sole, one and only person able to wield the power of your Bitcoins.
If you would like to hear me speak about this exciting topic, go to Brno, Czech Republic on February 19, 2019 to attend the second meetup from Blockchain Brno. I will also soon host a series of talks at the Learn By Doing meetup in Prague, Czech Republic.
Thank you for reading this far. If you have any questions or comments, please drop me a line on Twitter. I shall reply as soon as possible.
Stay tuned for the next article in which we’ll get all geometrical.